Modernising legacy without downtime. How to modernise a product without putting operations at risk
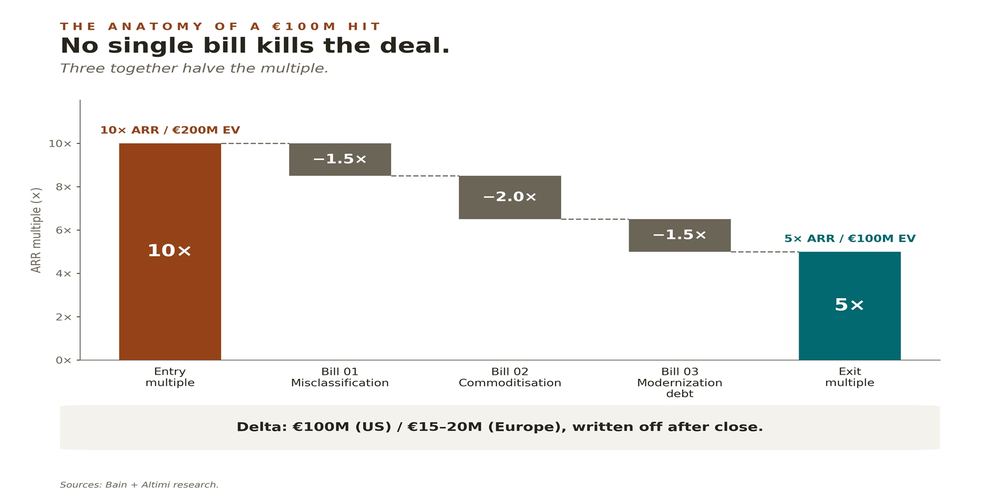
Only 1 in 10 PE funds follow the obvious. The rest risk €100M.

Legacy systems are rarely a problem just because they are old. Most often, their biggest limitation is that they still support processes that are critical to the business, while becoming increasingly difficult to develop, integrate, secure, and scale. Every change takes too long. Every deployment raises concerns. Every new feature requires more and more effort. At some point, the organization switches into a cautious “keep the lights on” mode, even though the product should be moving forward.
That is exactly when the question of modernization appears. And very often a fear comes with it: is it possible to modernise the product without stopping operations, without creating chaos in the teams, and without putting customers at risk? Our answer is: yes, but only if modernization is carried out in stages, deliberately, and with very strong risk control.
At Altimi, we do not see legacy modernization as a one-off “system rewrite” project, but as a product and operations process. One that improves the technology, reduces the risk of change, and creates the conditions for further growth at the same time. That is why we combine capabilities in product and application development, DevOps, cloud, managed services, as well as AI and data management. We apply this model every day as a technology partner for companies building and scaling digital solutions.
Why companies postpone modernization for too long
In practice, it is usually not about a lack of awareness. Teams typically know very well that the system needs to change. They see growing technical debt, dependencies on unsupported versions, architectural limitations, security risks, or performance issues. The problem is that the system still “works”, and the perceived cost of a potential production incident seems higher than the cost of postponing the decision again.
This is understandable, but only up to a point. The longer an organization waits, the more often it pays a hidden cost: slower delivery, more manual workarounds, harder deployments, greater dependence on a few individuals, and less predictable roadmaps. Legacy then starts blocking not only technology, but also the pace of the business.
That is why modernization should not start with the question “what do we rewrite?”, but rather “what is really limiting product growth today and where is the biggest operational risk?”. This distinction makes a huge difference. Not every old component has to be replaced immediately. Not every part of the system is equally critical. Not every architectural flaw requires a revolution. Good modernization starts with diagnosis, not with impulse.
The biggest mistake: treating modernization as a big restart
One of the most common mistakes is the “big bang” approach – assuming that the best solution is to rebuild everything from scratch and switch the entire business to a new version at once. This scenario looks good in presentations, but in a real product environment it usually means high risk, long wait times for results, and a dangerous accumulation of changes.
A legacy system almost never exists in a vacuum. It is connected to databases, integrations, operational processes, reporting, business logic, and the everyday work of users. When you try to replace everything at once, the number of unknowns grows. The scope of regression grows. The cost of testing grows. The likelihood increases that, instead of delivering value, the team will spend months re-creating in a new environment what already works in the old one.
That is why a phased model is far safer. One in which you first stabilise the foundations, then reduce risk in the most critical areas, then modernise subsequent layers, while ensuring that the product can continue to evolve. This is the logic we also apply in our projects: from discovery and consulting, through audit and modernization planning, to implementing changes in the application, infrastructure, and deployment process.
Modernisation without downtime starts with an audit
If the product is to be modernised without putting operations at risk, you first need to understand its actual state. Not the declared one. Not what was written down in documentation years ago. The real one.
That is why the first step should be a technical and architectural audit. The goal is to assess code quality, technical debt, performance, security, dependencies, deployment pipelines, integrations, compliance risks, and architectural constraints. Only then can you decide which elements require immediate action, which can be temporarily secured, and which are better modernised later.
In practice, this phase often changes the perspective. Sometimes the biggest problem is not the monolith itself, but the lack of regression tests. In other cases, the main risk is an ageing authentication layer, a single critical integration, or a release process that does not allow for fast, safe rollback. It can also turn out that the product can continue to evolve, but only after you stabilise environments and observability.
This is why we put so much emphasis in modernization projects on discovery workshops, technical assessment, and consulting. This is when you create not only a list of issues, but – above all – a sensible order of work. And without a good sequence, even the best team can fall into a costly and risky spiral of changes.
You do not have to modernise everything at once
One of the most important principles of safe modernization is: do not try to fix everything at the same time. It is better to split the program into several parallel streams, each with its own goal and risk profile.
The first stream is operational stabilisation. Here, the priority is to reduce the probability of incidents: monitoring, alerting, backups, rollback procedures, observability, environment quality, and the team’s readiness to respond.
The second stream is technological modernization. It includes upgrading frameworks, languages, libraries, databases, operating systems, frontend components, or authentication mechanisms. The goal is not “stack aesthetics”, but security, maintainability, and the ability to evolve further.
The third stream focuses on architectural changes. Sometimes refactoring selected modules is enough; sometimes it is about moving parts of the logic into separate services; sometimes it means introducing a new integration layer or API that offloads the old system core.
The fourth stream is product development around the legacy. This is crucial, because the business cannot wait six or twelve months for the technical transformation to finish. New features, integrations, dashboards, admin modules, or reporting flows can often be built alongside the existing system without destabilising the entire platform.
This is why modernization should be tightly connected to product engineering. Our approach to product and application development assumes not only building new web and mobile solutions, but also safely evolving existing platforms and modernising them in ways that do not stop the business. You can see this direction in our work, including an energy-tech application modernization project delivered without disrupting operations.
How to reduce deployment risk during modernization
Many organizations talk about modernization, but what they really fear most is deployment. And rightly so, because this is where most problems occur. Zero downtime is therefore not just a question of architecture. It is, above all, about how you run change.
Safe modernization requires test environments that are as close to production as possible, automated tests of critical paths, staged rollouts, feature flags where they make sense, precise rollback plans, and post-deployment validation. Hypercare is also very important – a period of increased support after release, when the team closely observes system behaviour and reacts quickly to anomalies.
These are not add-ons. They are the foundation. In practice, many projects do not fail at the moment of migration, but hours or days later, when hidden performance issues, unusual usage scenarios, or hard-to-reproduce integration errors appear. That is why good modernization plans for both making the change and safely “carrying it” after go-live.
At Altimi, we combine application skills with DevOps and SRE. As a result, modernization does not stop at upgrading a framework or migrating environments. It also covers rollback plans, CI/CD automation, operational documentation, monitoring, runbooks, and post-release support. This is how teams work that want to increase the pace of change without increasing operational risk.
DevOps and platform engineering are prerequisites for modern legacy
Many companies try to modernise applications while leaving the way they deploy and run them untouched. This is one reason modernization projects often fall short. Even the best code changes will not solve the problem if the organisation still operates with inconsistent environments, manual deployments, limited observability, and unclear ownership.
That is why legacy modernization must also include the operational layer. You need environment standards, well-designed pipelines, deployment quality control, meaningful monitoring, measurable reliability targets, and an incident response process. Where products are larger in scale, platform engineering is extremely valuable: an internal developer platform, golden paths, templates, and self-service for teams. This makes change less exceptional and more predictable and repeatable.
This is also why DevOps, cloud, and managed services are so important in modern modernization programs. In our projects, this combination includes CI/CD automation, cloud architecture, environment standardisation, managed services, SRE, and improving system reliability. As a result, the organization not only modernises the technology, but also builds the ability to develop the product safely in the future.
When modernization should also cover data and AI
For many organizations, legacy modernization is just the first step. Once the system becomes more stable, easier to maintain, and better integrated, there is room for further improvements: tidying up data flows, better analytics, process automation, user support with AI, or building new data-driven services.
This matters because a modern product is no longer just a “solid backend”. Competitive advantage increasingly arises at the intersection of applications, operations, data, and intelligent automation. Modernization should therefore create the foundation for further development, not just “fix old problems”.
At Altimi, we build this area through AI and data services – including data platforms, data pipelines, AI-driven automation, and AI-powered user support. These initiatives make sense when they are rooted in a stable architecture and well-structured delivery. That is why they so often appear after the first modernization phase, or in parallel, if the organization already has strong foundations.
What a mature modernization plan looks like
A mature modernization plan does not start with “we are going all in on microservices” or a decision to move everything to the cloud. It starts with understanding the impact on the business, continuity of operations, and product development speed.
First, you need to identify which parts of the system are critical for operations and revenue. Next, you identify the main sources of risk: security, performance, instability, technology dependencies, deployment difficulty, lack of tests, poor observability, or single points of failure. Then you decide which actions will deliver the greatest effect relative to risk and effort. Only after that does it make sense to choose specific architectural and technological patterns.
Often, the best solution is not a full cut-over from the old system, but a controlled way of taking load off it. In some projects, this means carving out new functions outside the monolith. In others, modernising the integration layer. In yet others, improving release quality and environments has more impact than deep architectural redesign. There is no single recipe. There is, however, one rule: modernization should reduce business risk, not increase it.
What the business gains when modernization is done right
Properly executed modernization does not benefit only the technical team. Its impact is felt much more broadly.
The business gains more predictable roadmaps because changes stop being a lottery. The product gains shorter time to market for new features because the cost of each change goes down. Operations become more stable through better monitoring, response procedures, and environment quality. The organization becomes more resilient to people risk because knowledge is no longer locked in the heads of a few individuals.
There is also a strategic angle. A modernised platform integrates more easily with other systems, supports security and compliance better, gives more flexibility in choosing growth options, and allows faster responses to market needs. This is why legacy modernization should not be seen as a maintenance cost, but as an investment in the organization’s ability to keep growing.
Modernisation without downtime needs a partner who understands the full context
The hardest modernization projects are not those with the most outdated technology. The hardest are those where you have to care about architecture, code quality, infrastructure, security, reliability, deployment processes, and the product roadmap all at once. This is why an end-to-end approach is so important.
At Altimi, we address such challenges by combining product and application development with DevOps, cloud, operations, AI, and data capabilities. This allows us not only to propose a direction, but also to go through the entire process with the client: from discovery, workshops, and audit, through application and infrastructure modernization, to post-go-live support and further product development. This approach is close to the technology partnership model, where the goal is not a one-off task, but a lasting strengthening of the product and the organization.
How to modernise without stopping the business
Legacy does not have to be a ball and chain. It can become the starting point for a structured, safe, and well-planned transformation. There is one condition: you cannot treat modernization as a one-off rewrite under pressure. You need to treat it as a process that balances the needs of business, technology, and operations.
Zero-downtime modernization is, in practice, a mix of good assessment, the right sequence of actions, deployment risk control, mature DevOps, and conscious product development. When these elements work together, the organization not only modernises the technology. It also gains something far more valuable: the ability to keep growing without constant fear that any change might stop the business.
FAQ – zero-downtime legacy modernization
Does modernizing a legacy system always mean rewriting the application from scratch?
No. In most cases, a full rewrite is not the best option. It is costly, slow, and operationally risky. A phased modernization, where you first identify the most problematic areas and then gradually improve architecture, upgrade technologies, and develop new features in a controlled way, usually works much better. This approach helps minimise downtime risk and maintain product continuity.
How do you modernise a product without stopping operations?
The key is to break work into stages and combine application changes with solid deployment practices. In practice, this means a technical audit, setting priorities, preparing environments, building automated tests, defining rollback plans, monitoring after release, and hypercare support. Safe modernization is not one big change, but a series of well-planned steps that minimise the impact on users and business processes.
How do you know when a legacy system needs modernization?
Typical signals include rising maintenance costs, slower development, difficulties in delivering new features, integration issues, dependencies on unsupported versions, increased security risks, and the team being afraid of every production change. If product development is limited more by technology than by business strategy, it is usually a sign that modernization is due.
Does legacy modernization only concern application code?
No. Effective modernization covers much more than code. Infrastructure, deployment process, security, monitoring, environment quality, observability, and change management are often just as important. That is why modernization must bring together application development, DevOps, cloud, and operational capabilities. Only this kind of approach delivers lasting results and truly reduces risk.
What business benefits does legacy modernization bring?
Well-executed modernization improves roadmap predictability, shortens time to market, stabilises environments, and reduces the cost of future changes. It also makes integrations easier, strengthens security, reduces dependency on outdated technologies, and gives the organization more flexibility in scaling the product. In practice, it means the company can grow faster without constantly fearing that each change will threaten operations.
Where is the best place to start with a legacy product modernization?
The best starting point is a technical and architectural audit combined with a business impact assessment. This step helps identify where the biggest risks are, which elements need urgent attention, and how to plan the sequence of actions. Only then does it make sense to build a modernization roadmap that includes both technology changes and measures to safeguard deployments and support future product growth.