Tech Due Diligence for M&A: code, architecture, security, team
How engineering teams turn AI from a coding shortcut into a structured delivery system –
and what phased, human-first modernization looks like in practice.

Why Tech Due Diligence matters in M&A
In mergers and acquisitions, technology is often either the biggest value accelerator or a hidden risk that only surfaces after the deal is signed. Tech Due Diligence (TDD) has one goal: to identify technology risks and costs before they become problems, and to assess whether the product and engineering organization can sustain growth post-transaction.
Well-executed TDD is not just a code audit. It is an assessment of:
- quality and maintainability of the solution
- architecture and scalability
- security and compliance
- maturity of DevOps and operations
- competence and stability of the team
- and the real costs: technical debt, migrations, refactors, and maintenance.
Below is a practical checklist you can use as a foundation for Tech Due Diligence – both when acquiring a product company (SaaS) and when evaluating a software “build-up” within a larger business.
Scope and context (before you even open the code)
Goal: understand what is being acquired and how technology supports (or blocks) the business.
- What are the key products/systems (core vs. supporting)?
- Which critical business processes does the system support?
- What is the revenue model, and which parts of the platform are revenue-critical?
- Which components are single points of failure?
- What does the roadmap look like and what are the commitments to customers (SLA, contracts)?
- What are the dependencies on vendors (cloud, licenses, third‑party services)?
Outcome: a system map plus risk priorities – i.e., where TDD should “dig” the deepest.
- Codebase & Engineering Quality
Goal: assess maintainability, regression risk, and the cost of further development.
Repository structure and code hygiene
- Do repositories have a clear structure and ownership?
- Are there coding standards, code review practices, and a style guide?
- Is there consistency in naming, modularity, and separation of layers?
- What does the technical debt look like (TODO/FIXME, legacy modules, “hot spots”)?
Testing and QA
- Which types of tests exist (unit/integration/e2e)?
- What is the real coverage of critical paths (beyond raw coverage %)?
- Are tests stable (flaky tests) and run in CI?
- How often do regressions occur after deployments?
Dependencies and vulnerabilities
- Are dependencies updated regularly?
- Is there a process for managing vulnerabilities (SCA)?
- Are there end‑of‑life components (frameworks/libraries without support)?
Technical documentation
- Is there a meaningful README, runbook, and contribution guide?
- Are architectural decisions documented (ADRs)?
- Can a new engineer be onboarded in a reasonable time?
Red flags: no tests, no CI, heavy reliance on tribal knowledge, manual deployments, a high number of critical vulnerabilities in dependencies.
- Architecture & Scalability
Goal: assess whether the system can handle growth and how costly integration or modernization will be.
Application architecture
- Monolith or microservices – and is the choice justified?
- Are domain boundaries (bounded contexts) clearly defined?
- How are data consistency and transactions handled?
- Where are the bottlenecks (single database, single service, single queue)?
Data architecture
- Which databases are used and why, and are they used appropriately?
- Are there caches, indexes, and query optimizations?
- Are there issues with data quality, duplication, or inconsistency?
- Are there data pipelines / integrations, and how are they maintained?
Performance and reliability
- Are there SLOs/SLAs and real uptime metrics?
- What does observability look like: logs, metrics, traces?
- Is there a disaster recovery (DR) plan, backups, and restore testing?
- How does the system handle traffic spikes?
Integrations and dependencies
- What are the critical integrations (payments, ERP/CRM, providers)?
- How resilient is the system to provider outages (retries, circuit breakers)?
- How are API versions and backward compatibility managed?
Red flags: no monitoring, no DR tests, no scaling strategy, “accidental” architecture, dependence on a single non‑redundant component.
- Security & Compliance
Goal: assess incident risk, audit readiness, and impact on the transaction.
IAM and access
- Is there SSO/MFA? How are permissions managed?
- Are there shared accounts and a lack of auditability?
- Is access to production controlled and logged?
Secrets and keys
- Are secrets stored in a vault/secret manager or in code?
- How are keys rotated and who has access?
Application security
- Are SAST/DAST/SCA integrated into CI/CD?
- Are regular penetration tests performed?
- How are vulnerabilities and patching managed?
Data and privacy
- How is sensitive data (PII) protected?
- Is data encrypted at rest and in transit?
- Are there data and log retention policies?
Incidents and operational readiness
- Has the company experienced security incidents, and how did it respond?
- Is there an incident response plan (IRP) and regular exercises?
- Is anomaly monitoring in place?
Red flags: secrets in repositories, no MFA, no patching process, no vulnerability management, no audit logs.
- DevOps, Cloud & Operations
Goal: assess whether the company can deploy and operate the system safely.
- Is there CI/CD? What does the release process look like?
- Is infrastructure defined as code (IaC)?
- Are environments (dev/stage/prod) reproducible?
- What do monitoring and alerting look like?
- Are there runbooks and incident response procedures?
- How are run costs managed, and is there any FinOps practice?
Red flags: manual deployments, “click‑ops” infrastructure, no rollback strategy, no non‑prod environments, heavy dependency on a few key people.
- Team & Engineering Organization
Goal: assess the ability to maintain and evolve technology after the acquisition.
Structure and skills
- Which roles are present (backend/frontend/QA/DevOps/data/security)?
- Are there strong technical leaders and a clear decision‑making process?
- How is product management organized and how is the backlog handled?
Stability and personnel risk
- Who are the single points of knowledge?
- What is the turnover like and how dependent is the company on contractors?
- Are there onboarding processes and documentation?
Engineering culture
- Are there code reviews, quality standards, and tests?
- How is technical debt managed?
- Are there retrospectives and continuous improvement?
Red flags: no QA/DevOps, no technical leadership, knowledge trapped in a few heads, high churn, chaotic backlog.
- Licenses, IP & Legal Risks (often overlooked)
Goal: assess IP risks and licensing costs.
- Does the company own the code (contracts with employees and contractors)?
- Which open‑source licenses are in use, and are they compliant with policy (e.g., copyleft)?
- Are there commercial components/licenses with a risk of cost escalation?
- Are there patents or third‑party IP embedded in the product?
What a good Tech Due Diligence outcome looks like (a format that actually helps M&A)
A good TDD should end not just with a list of issues, but with a decision‑support map:
- Critical risks (deal breakers) – e.g., serious security gaps, lack of IP rights, inability to scale.
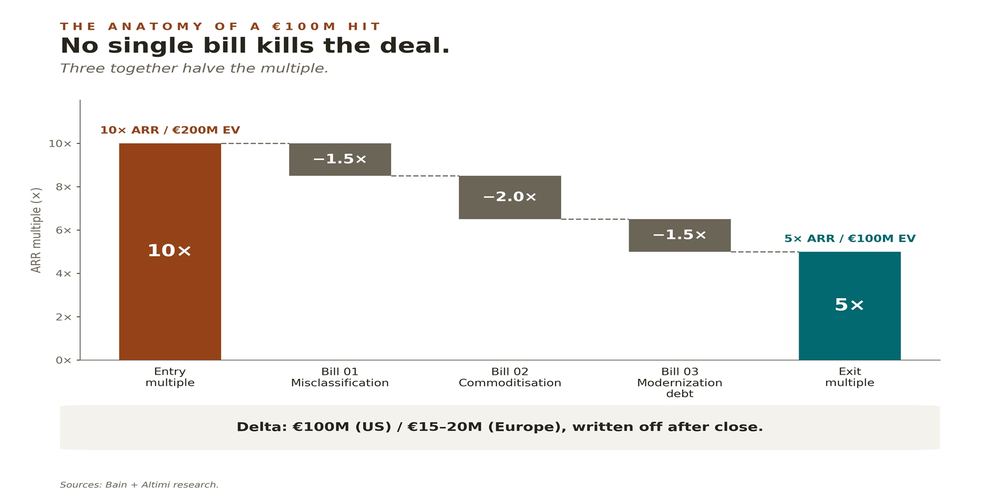
- Material risks (for valuation) – technical debt, required migrations, DevOps gaps.
- Operational risks (for integration planning) – processes, team, monitoring, onboarding.
- A 30/60/90‑day post‑acquisition action plan – what to do first to stabilize the situation.
- Cost and effort estimates – what it will take to bring the technology up to “standard”.
Where Altimi can help: Tech Due Diligence as part of a partnership
In a partnership model, Tech Due Diligence does not end with the report. The real value appears when the audit flows directly into execution: stabilization, modernization, security improvements, and delivery alignment.
In practice, Altimi supports organizations in:
- analyzing architecture and code quality
- assessing and implementing DevOps/CI/CD, IaC, and observability
- raising the level of cybersecurity (IAM, secrets management, scanning, processes)
- assessing team maturity and providing organizational recommendations
- and executing remediation plans in consulting / managed services / BOT models.
FAQ: Tech Due Diligence for M&A
Is Tech Due Diligence just a quick code review?
No. Code is important, but TDD also covers architecture, security, DevOps/operations, run costs, licensing dependencies, and organizational risks (such as single points of knowledge). The goal is to quantify post‑acquisition risk and cost.
What are the most common technological deal breakers?
Most often: lack of IP ownership (e.g., contractors without IP assignment), critical security gaps and lack of basic processes (MFA/monitoring), inability to scale or extremely costly modernization, and strong dependence on one or two key people without documentation.
What should a TDD deliverable look like to be useful for executives and investors?
The best format includes: risk classification (critical/material/operational), impact on valuation and integration plan, remediation cost estimates, and a 30/60/90‑day plan. That way, TDD is not “a report for IT” but a concrete input into the transaction decision.